Introduction to IoT Capabilities:
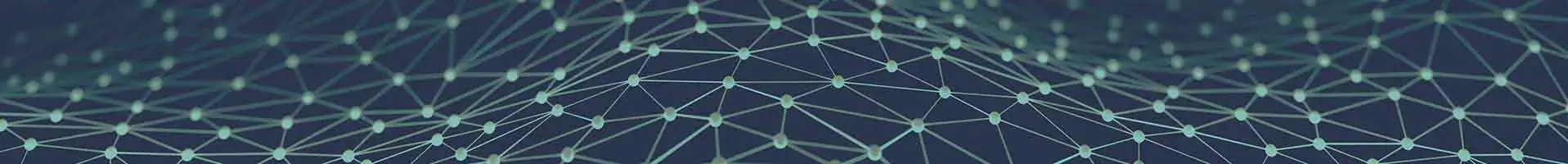
In this type of IoT platform, normally what they mean is they can do set and get on the end devices so to collect data from them and to control them and from the IoT platform and there are portals maybe sometimes where you can see inventory you can most of the time do big data or bi analysis rules and automation and connect applications to it and sometimes most of the time you can do some basic firmware update again not necessarily to the end devices because a lot of them don't have the firmware update capabilities.
IoT Device Management:
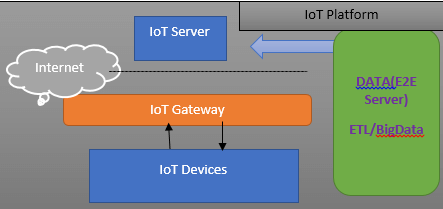
When we're talking about IoT and device management if a little bit more interesting so an IoT device management platform first of all there's the gateway device management in the middle so don't forget that these things are quite big quite complex they're collecting data from sometimes thousands of tens of thousands of devices their data model the amount of data that they're holding is both complex and dynamic because there's always the add and remove components you need to be able to do the agnostics and repair.
Because these things might be there might be millions of them in a cross-like you know a state or a country where some of them might be far away you don't want to be you don't want to need to send a technician you do an IoT installation this thing should hold for tens if not you know more than that of years and you need to be able to configure things from a central location this is not simply like you know it when you have a simple smart building installation and you are the owner of the building you are the one that is managing it you can just log into the gateway embedded web page configure whatever you need to configure.
Security in IoT is a very important field. Ignore this in any applications will source a lot of issues for your customers and you will have a lot of issues selling other products. You need to understand the security issues.
Why Security is Important in IoT?
In IoT security is important in general but when it comes to hardware and things that control hardware, it's precisely and particularly very dangerous. Then how to secure an IoT device and how to secure a network and how to manage updates to software. So why is IoT security important? In IoT one of the words is “things”, so if security issues would affect software up to now, you now have things that rely on software and that interact with the environment. So, security issues migrated from the cyber wall to the real world through Internet of Things. Internet of Things (IoT) is everywhere like as I said every field will use software and connection to the network. Endpoint devices like Macs also face growing security risks, and applying expert-approved techniques for malware detection and removal provides an additional layer of protection. So, a security breach in one of the components is a security breach in the real world. Here are some security examples:
So, as I said up to now it was a cyber-problem only software but if you use apple home kit, your door locks, car lock is controlled by the internet but it's something that is connected to the Internet. An attacker will simply unlock your door house. Your house appliances are connected to the Internet.
They burn their physical devices somebody can make your printer burn, your microwave oven burn, your fridge burns if they change the software and control it in a different way something might actually blow up.
Then again if you have a fridge, you might be surprised that it's actually mining bitcoins or its crashing servers all over the world and you just have the impression that the fridge is cooling your food, but in fact, it's compromised and its software is doing something totally different and there's no way that you can find out unless you're an IT specialist and you can watch your internet traffic you have no idea what your fridge does when it's alone at home. Medical devices imagine hacking pacemakers.
Somebody might die because of the hacking of a medical device and you have medical devices which are controlled over wireless and somebody on the street can have a problem. Public utilities you can shut down the power grid, the water supply this is really dangerous like connecting these devices to the Internet is a bad idea in general but then again you cannot go against the trend. So, if you connect them, keep in mind that security is particularly important when it comes to things.
Visit us to get an awareness for tackling the problem and ensure that both related hardware and software are secured.
Security by Design vs. Security by Obscurity:
The Law of security is you always want security by design, not by obscurity. Ninety percent of the security today is done by obscurity meaning if there's Java development company that has a closed box and that does security. They think if no one knows how this box is made then no one can break it so it's secure and that’s true if you don't know how it's made it’s more difficult to break it. But somebody will and if they break one they break all of them and moreover because somebody broke it it's particularly difficult for companies that do security to protect it because the only ones that know how it's made is the attacker and its producer. If the producer is not able to secure it and he wasn't in the first place nobody can help you.
When it’s security by design usually it's an open product like the security thing is not that no one knows how it's done but everybody knows. It's theoretically proven or mathematically proven that it's secure. They use some means to secure it which are open, and the security comes from some mathematical process usually. If somebody compromises this thing it's easy to fix because not only the provider can do it, but anyone anybody in the world can do it. Examples are “SSL/TLS “was broken several times but the community fixed it immediately. As soon as the vulnerability showed up, they knew how to fix it.
For a black box, this is difficult. So always keep in mind security by design, not by obscurity. This is the way to go companies start to migrate towards this.
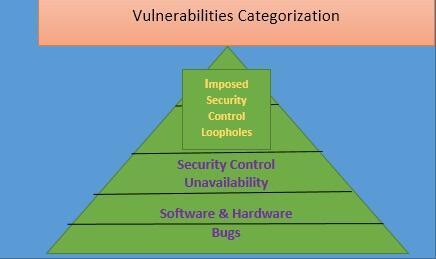
Categorizing the Security Challenges in IoT:
There may be various challenges while enforcing the IoT securities.
Resource Limitation:
Embedded System with traditionally security solution imposed
Security resources may be limited
Lack of Security perimeter:
Lack of firewall may cause physical attacks
A device may be located outside of the security perimeter
This is subject to the proximity attacks
Miscellaneous:
Difficulty in Maintenance.
Offline security updates may not be possible
The lifecycle may be too long if the operation is fully automatic
Security Principles are measured by the efficiency of blocking unauthorized use and access and the efficiency in protecting the IoT devices/systems from cyber-attacks. This ensures data protection and encrypted communication as well as ensuring that no malware is installed. The devices must be integrated with the security management system for detecting all types of cyber events and network events.
fundamental principles of security that are needed we need to make sure that only authorized users processes you know other devices are allowed to communicate and control the devices that we've got protection against basic cyber-attacks that malware can't be installed on the device that the data cannot be easily stolen off the device that the operation of the device can't be manipulated or interrupted and then finally we need to make sure that these devices aren't just islands and that's one area of cyber security in the IoT space that's often been overlooked the devices need to be able to detect and report if they are being probed you know if somebody starts to try multiple login attempts against the device.
if somebody starts to access ports that aren't normally accessed on the device all those things are precursors to cyber-attacks you know the initial stages of an intruder trying to make penetration into a network and so we need to be able to report that back to a management system so that we know these attacks are going on and can take action to block them and that's another really important piece that's often overlooked.
By building security controls into the device. These are the same security measures that you take on any device if you’re looking at a laptop, it’s going to have the ability to perform an authentication. It's going to have secure boot processes it's going to have a secure firmware update process. It's got a firewall built into it so that you can control what messages are received by the device and it can have again that additional layer of protection. So you need to look at how do you build these capabilities into your device and that has to start early in the design process.
Java-Based Security Solutions for IoT:
The predominant factor in IoT systems is security Solutions and these solutions must be implemented in IoT devices to make them secured. These security solutions include:
Authentication and Authorization (oAuth2/JWT Web Token-based)
Secure bootup process
Updates must be secure
There should be an Embedded Firewall for IoT systems
Monitoring the Security and the Management through any management console
Data encryption should be enforced
Sectigo:
One way that you can do that is to work with Sectigo. It is one of the leading cyber security providers of embedded security solutions and digital identity solutions for IoT devices. So they provide some very robust mature solutions that are being used by many different companies to add security to their device and again its solutions are built specifically for IoT devices that are designed to be highly portable and to work with a wide range of devices and this allows you to standardize on a single set of technologies that can be used across all of your devices. In addition to the embedded solutions provided by Sectigo, they are also a PKI provider. They provide certificate issuance solutions that are designed and scalable for IoT device use cases. Modern approaches such as RAID cyber security techniques emphasize structured methods for detecting, reporting, and mitigating intrusions at scale, ensuring IoT systems are resilient even in complex environments.
How can IoT devices be secured?
1. Local Security
2. Network Security
3. Software & Hardware Security
So, how do we secure the device? Here the focus is on local security like what happens on the device. Network security, software that runs on the device and then about the hardware security that runs on the device.
Local security:
Change the Default Password:
Disable Unused Services
SSH Login Process, X Server UI or Default Login or Device Discovery (Avahi)
This is simple. First of all, change the default password like for the Raspberry pi, if you have a device with the raspberry pi and take the image of the raspberry pi it's pi and raspberry. If you don't change this anybody can break into it for the BeagleBone, its Debian and “temppwd”. There are several devices commercially sold which never cared to change this data. Suppose if you buy a router, a wireless router, how you find your password by default it's the same as you just go online type the name of the router default password and you find it. Surprisingly, many people will not change that.
Secondly never make a default password based on something on the device by the MAC address or something else like really when you deploy a device, find a way to put a random password and that's a random password. Another thing is you need to be careful about the random generator. Secondly disable all unused services like if you buy a Raspberry Pi and take its normal image, it's full of services for development production devices, and they don't need SSH. SSH is not something that you on the device.
Usually, they have no user interface disable it meaning delete the files and secondly disable the default login if you buy a Raspberry Pi, it boots up with the graphic interface never asks you for a password. So, disable that. Another service is avahi. Avahii: is a discovery service that we have used to discover the Raspberry Pi. Once it goes into production if you don't need it and usually you don't forget it just turn it off. When an attacker doesn't need to know what the IP of your Raspberry Pi is.
Software Security:
Use Supported software (Make sure software is supported and its producer should keep the software up to date)
upstream Changes: If you change any software then should push it to upstream means the public kernel with good practice of Opensource so that everyone can use it. ( For Every software update, you have to port your software for it)
Use opensource Libraries (Use a library that is actively maintained and updated on a yearly or half yearly basis that means developers should follow the security updates for the Library)
Software updates should include feature update as well as Security Update
Network Security:
Avoid Self-written protocols
Use Secure Protocols like:
HTTPS: Authenticates the server
Encrypted Communication
MQTT or SSL Communication Protocol:
Encrypted MQTT
XMPP: Authenticates Servers between each other
Network security is really important and it's not breaking in into the device it means how you communicate over the network and it doesn't matter if it's the local network or the internet it still should be the secure local network you would say it's only the local network if it's not on cable, somebody might sniff packets and with enough amount of time he might be able to get your communication so be careful if you're sending over-the-air it doesn't matter if it's a local network think of it as a public network. Effective network orchestration ensures that IoT systems maintain seamless communication while bolstering security through optimized control of data transmission. first rule avoid self-written protocols.
If you need to communicate with some device do not write your protocol why not because you're the only one using it you are doing security by obscurity people will not know how your protocol is but it's breakable it's easily breakable no one except you is testing this so there's not a huge amount of users that will test the protocol is it theoretically secure did you mathematically prove it no firewalls might stop your protocol so if a firewall is small enough it will simply cut your protocol out so avoid using that use protocols which are known for this and securely use them so if you do HTTP use HTTPS why HTTP does two things the easiest one is it encrypts traffic so your traffic flows through the internet.
But it's encrypted secondly super-important it off the server so before sending one bit of data it will ask the server to authenticate itself with a certificate so you can be sure that some that server is the one that you need otherwise if somebody breaks a DNS they can fake a server super easy to use HTTP MQTT use it over SSL SSL will ask the MQTT server to provide a certificate before it communicates with you so you can be sure that you are communicating with the server that you want and not a fake one.
Secondly again it encrypts traffic an XMPP if you need a more complicated protocol do not use the TCP socket use XMPP will exchange messages between devices in a secure way why it authenticates the server it authenticates the device to the server and if it needs to send data to a device that is not connected to the same server it will authenticate the other server before actually sending the data in contrast with a lot of other protocols like Internet Relay Chat. XMPP makes sure that if it contacts another server. It's a server that he wants to contact and not a fake one when it comes to devices. If you call if you connect it to the internet using a computer, not a microcontroller.
Conclusion:
Here, I have explained in detail the types of Security challenges and types of various security vulnerabilities illustrating Association, Aggregation and Composition and Inheritance in Java.